TPM Passthrough in Linux Virtual Machine Manager (virt-manager)
Hi everyone,
Today, we will see how to pass our TPM (Trusted Platform Module) from our machine to our QEMU/KVM virtual machine using the Virtual Machine Manager tool. We will also modify an AppArmor configuration file to allow access to it. This is needed mostly if you plan on using Windows 11 as a virtual machine, unless you use a method to patch a Windows 11 ISO image in order to install it.
Once Windows 11 is installed, the TPM is not really required, but these steps will make it appear in your VM regardless and provide better security to the OS.
Adding the TPM module to our Virtual Machine
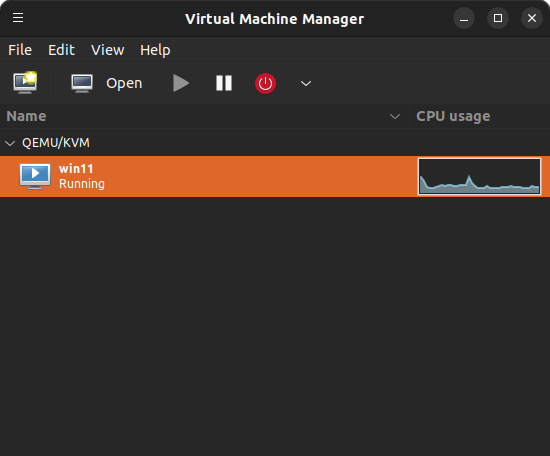
We’ll start by launching the Virtual Machine Manager tool:
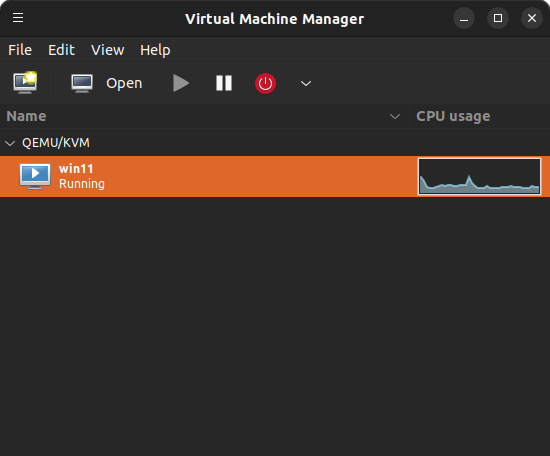
There, we will double click on our machine. This will open our VM console. Then, we will go to the “View” menu and select “Details” to bring our machine configuration:
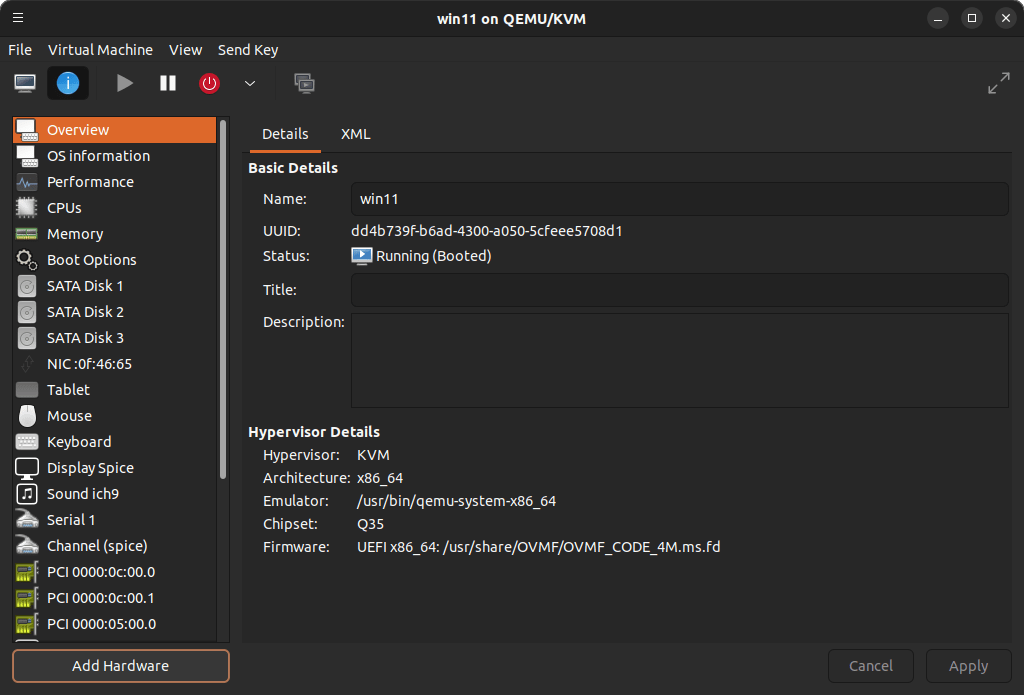
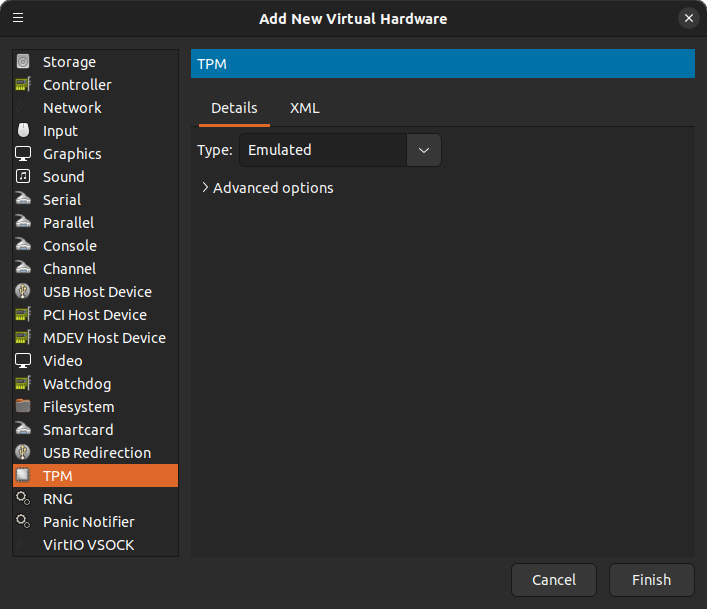
Click on “Add Hardware”, and select “TPM” from the list that will be shown:
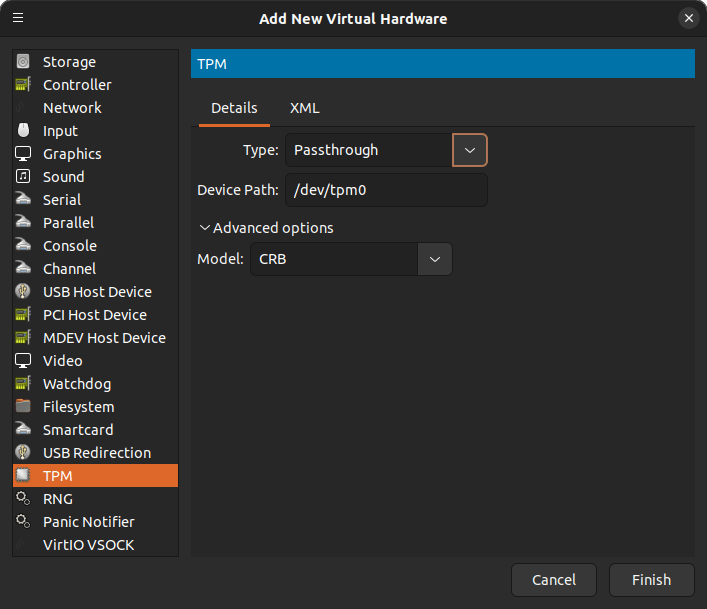
We will change the Type to “Passthrough”. In the Device Path, our TPM device should be “/dev/tpm0”. Click “Finish”:
Editing the AppArmor libvirt-qemu file to allow access to our TPM
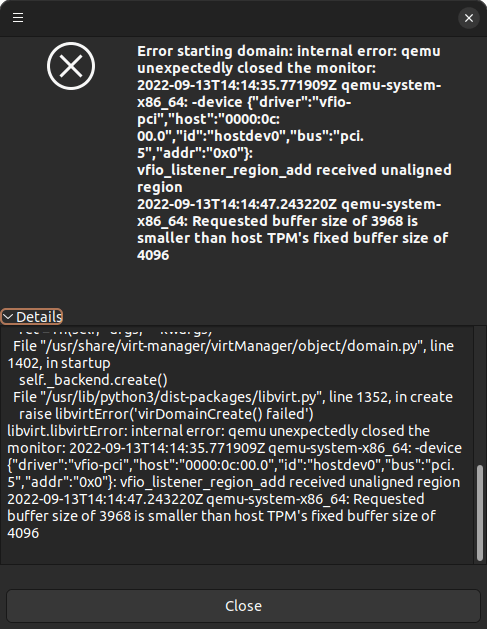
If we attempt to start our VM, we may be presented with this message:
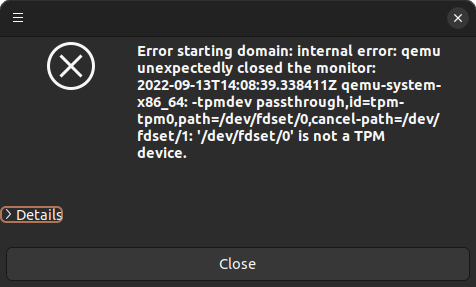
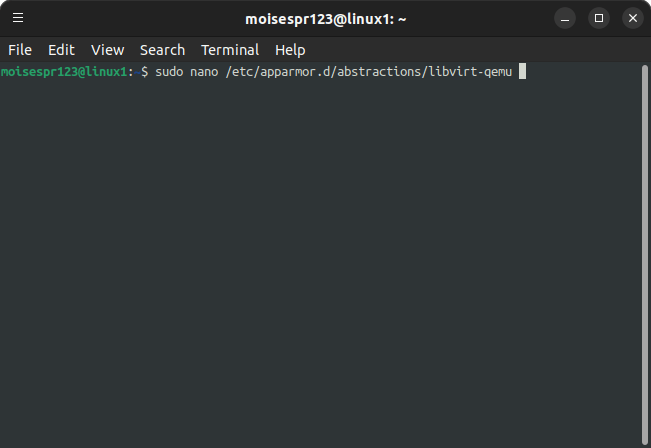
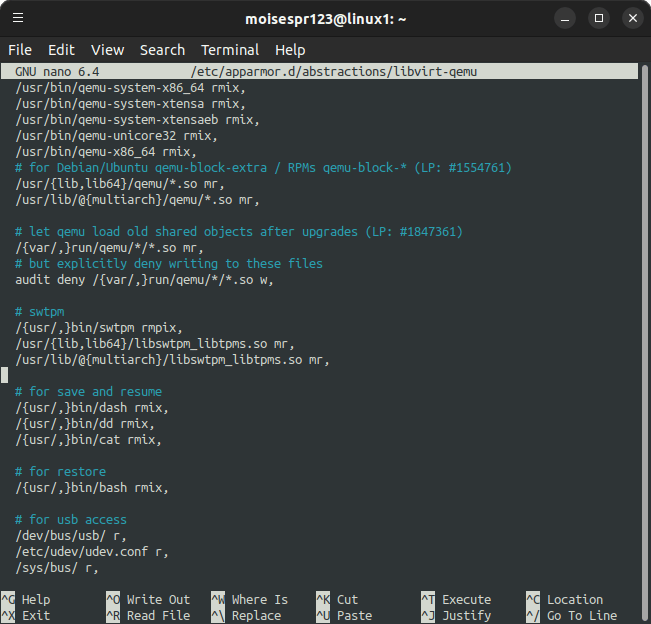
First, be sure that you have the TPM module enabled in your BIOS. If it is, then we may need to update the AppArmor libvirt-qemu file to allow QEMU/KVM to access the module. For this, we will load a terminal window and edit the file /etc/apparmor.d/abstractions/libvirt-qemu. I’ll use nano to edit it:
Scroll down to the part where it mentions swtpm (Emulated TPM section):
Add below the following. You can add a comment line to let you easily identify this section:
# TPM Passthrough
/dev/tmp0 rw,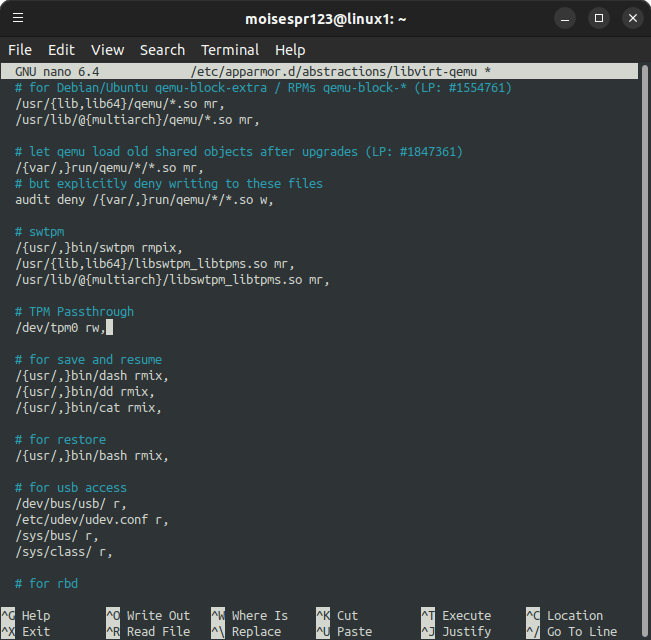
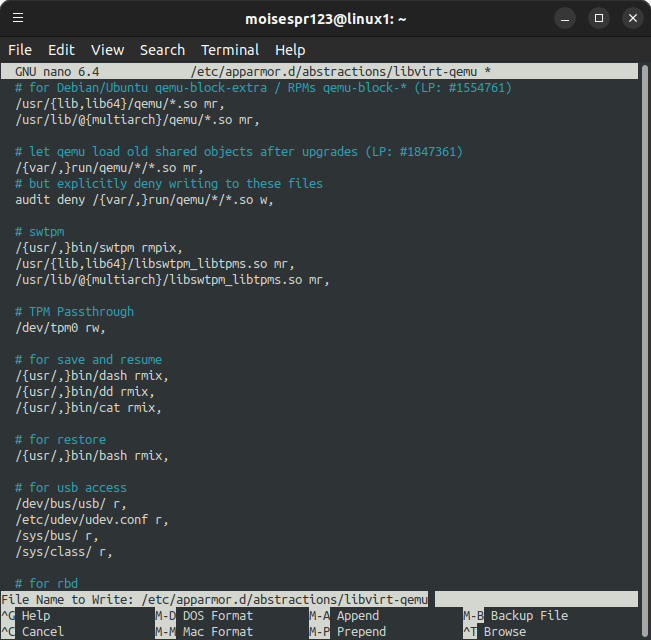
Save the file pressing CTRL + O and pressing Enter:
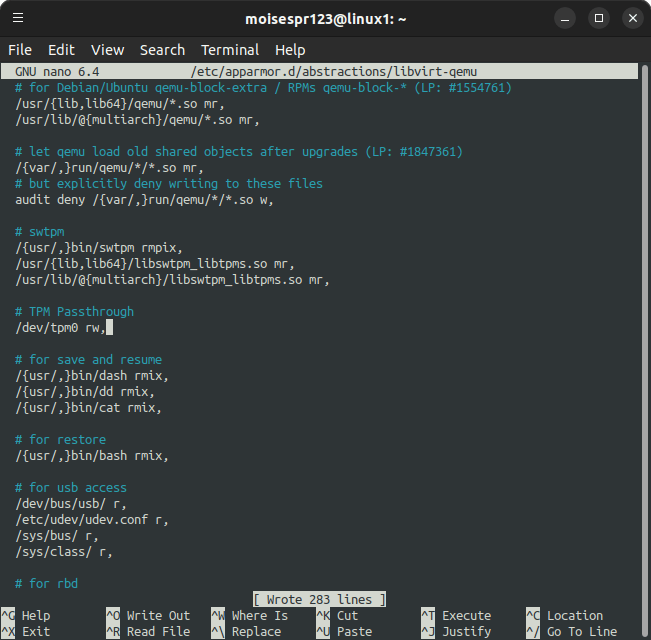
Exit nano by pressing CTRL + X. Then, restart the AppArmor service with:
sudo service apparmor restart
Now we can attempt to run our VM.
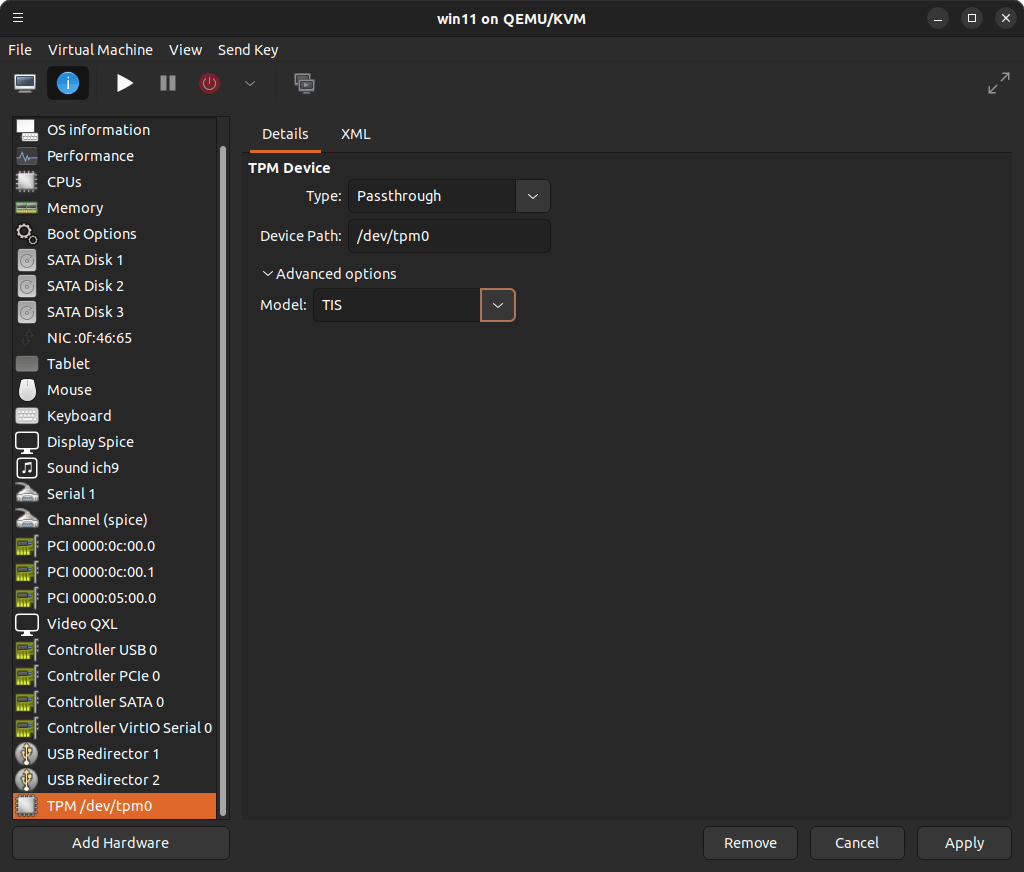
You may be presented with another issue:
In this case, you can easily overcome this by changing the Model type from CRB to TIS:
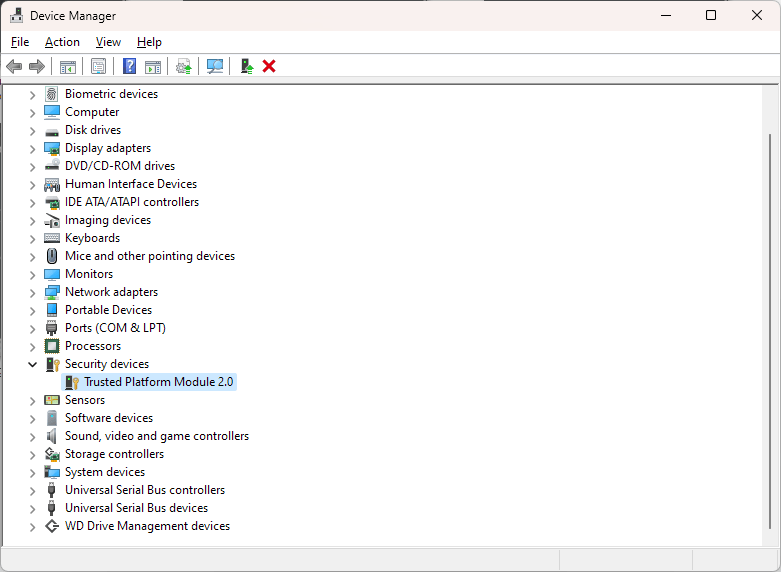
Now, boot your VM again, and you should now have the TPM module inside it: